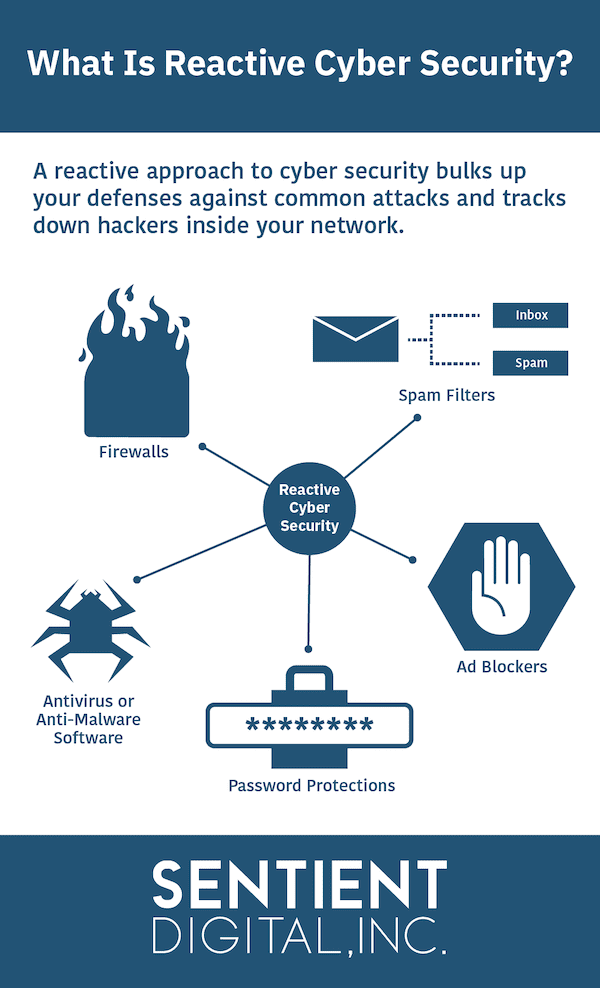
Cybersecurity Prism - ✴✴What is proactive vs reactive cyber security?✴✴ Proactive cyber security involves identifying and addressing security risks before an attack occurs, whereas reactive cyber security involves defending against attacks that

Relationship between passive, proactive and reactive response using... | Download Scientific Diagram
![PDF] Proactive vs. Reactive Security Investments in the Healthcare Sector Proactive vs. Reactive Security Investments in the Healthcare Sector | Semantic Scholar PDF] Proactive vs. Reactive Security Investments in the Healthcare Sector Proactive vs. Reactive Security Investments in the Healthcare Sector | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1fcf353f878db23be00edc443625bf3ef3d94b73/34-Figure1-1.png)
PDF] Proactive vs. Reactive Security Investments in the Healthcare Sector Proactive vs. Reactive Security Investments in the Healthcare Sector | Semantic Scholar

Proactive vs. Reactive: How Savvy Use of Analytics Helps Contact Centers Navigate and Adapt to Uncertainty | NICE

Knowing the Difference Between Proactive and Reactive IT Support | Managed IT Services and Cyber Security Services Company - Teceze