
The Kill Chain: Defending America in the Future of High-Tech Warfare : Brose, Christian: Amazon.es: Libros

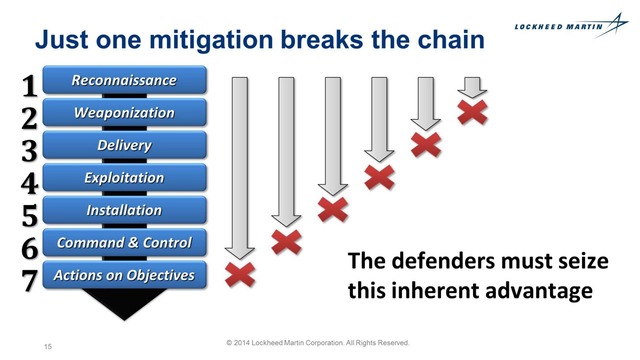
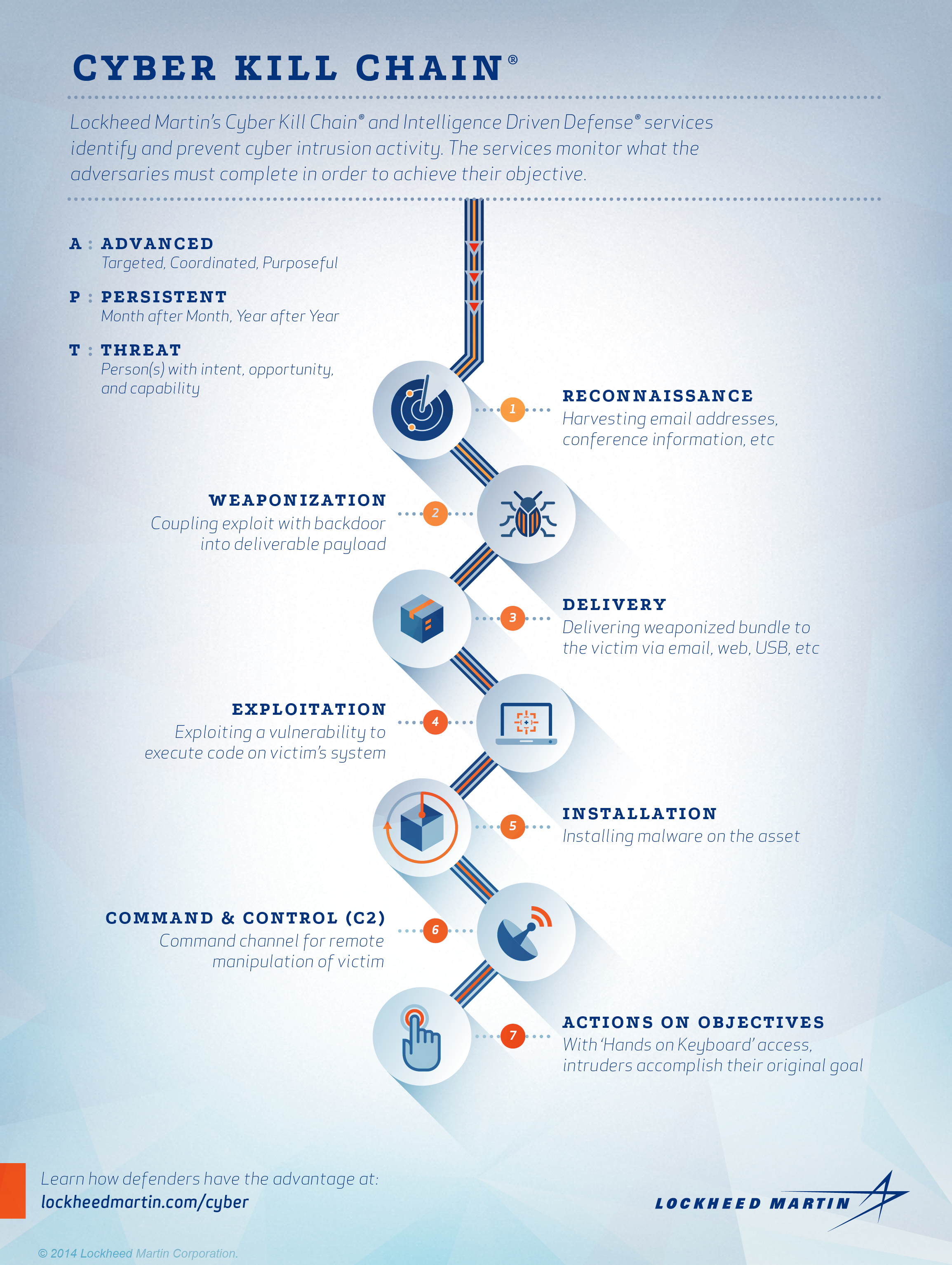
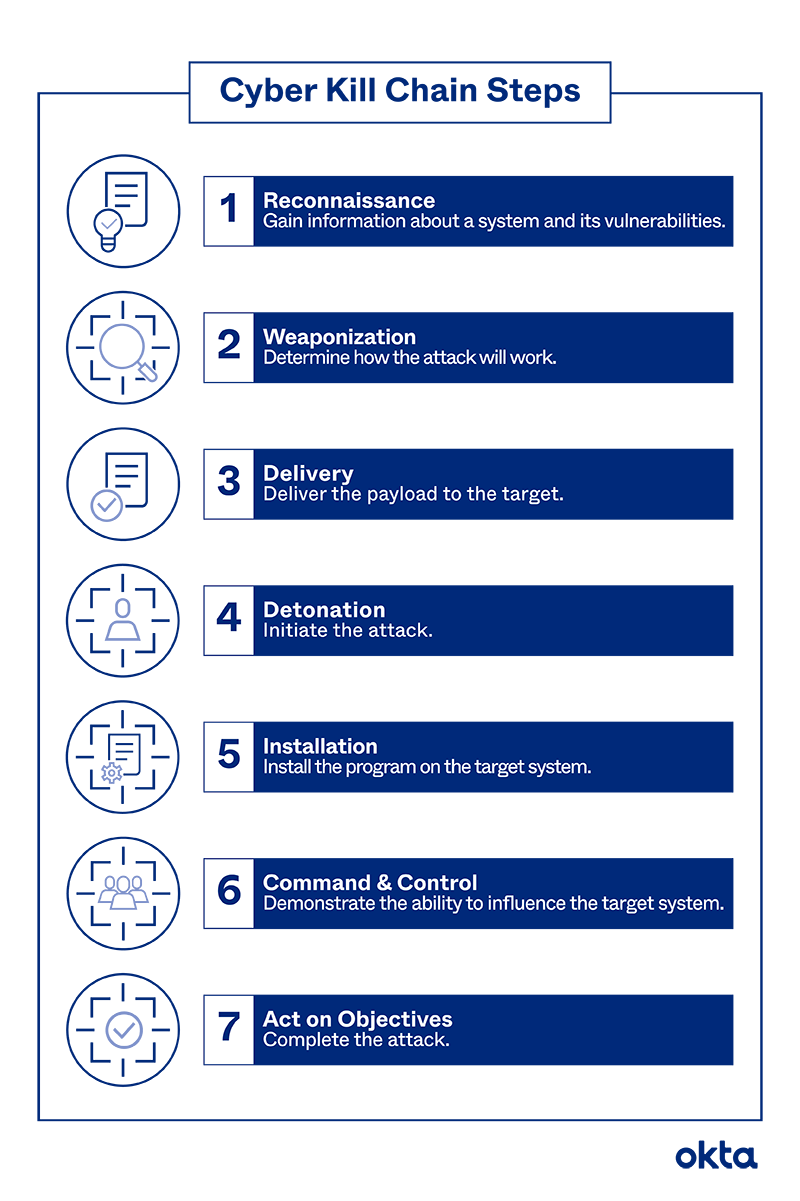
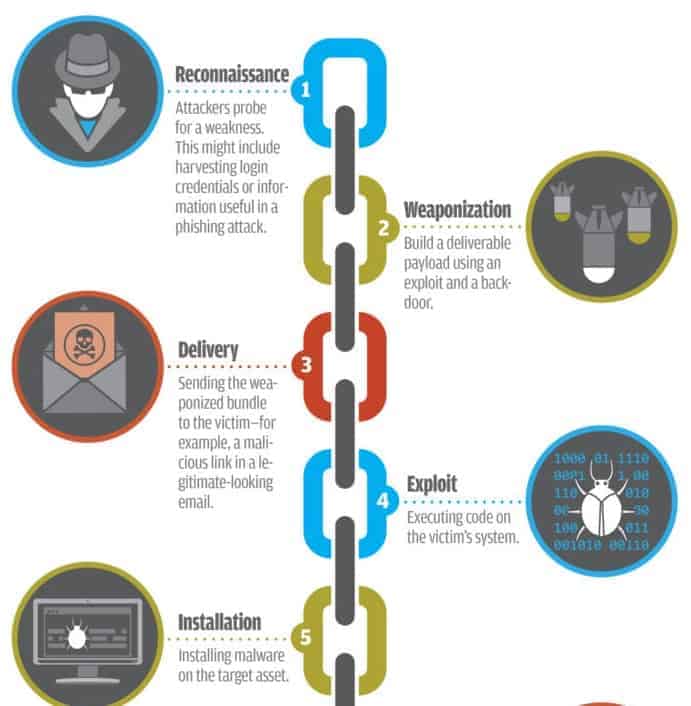
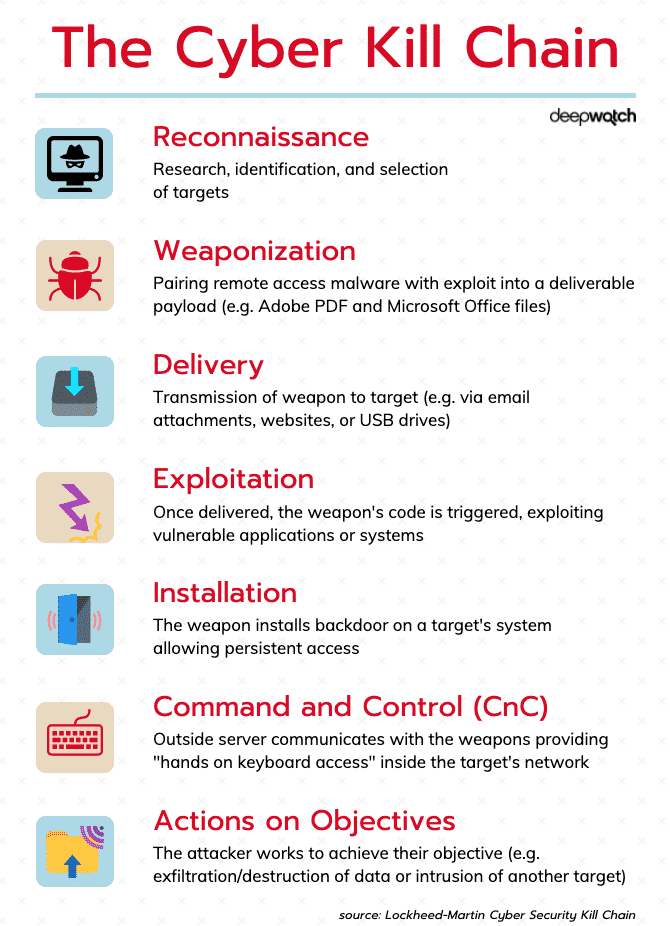
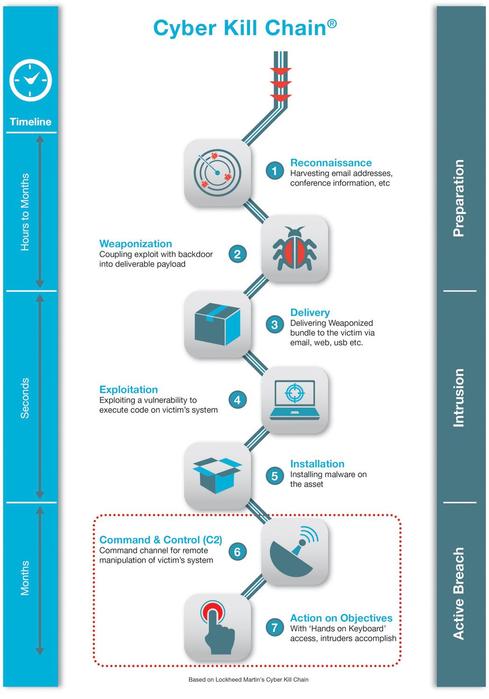
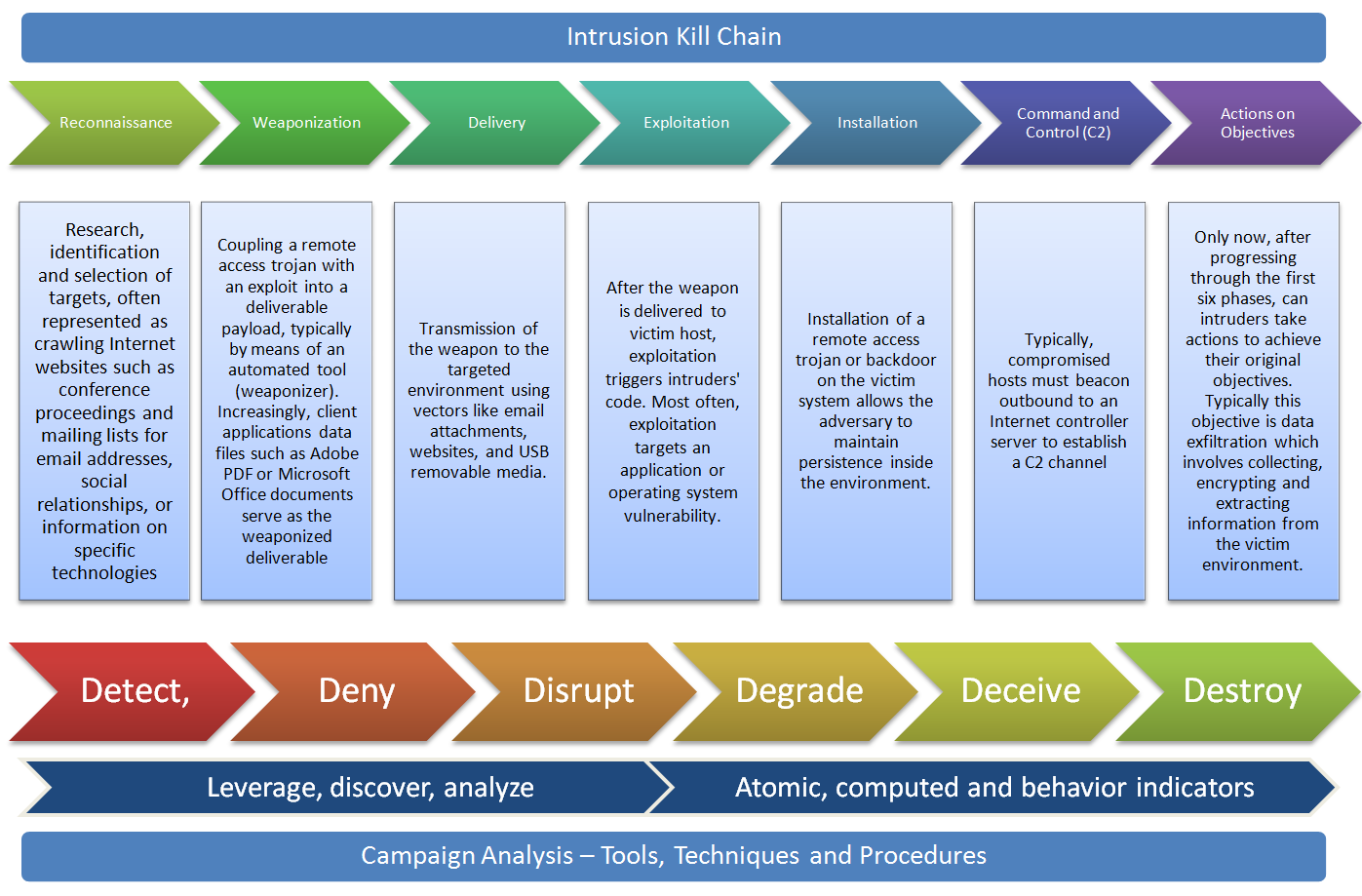
BizBrolly - We Build Software for Mobile and Web - The term “Kill Chain” is originally a military concept that defines a structure of an attack. In simple terms, Cyber kill chain
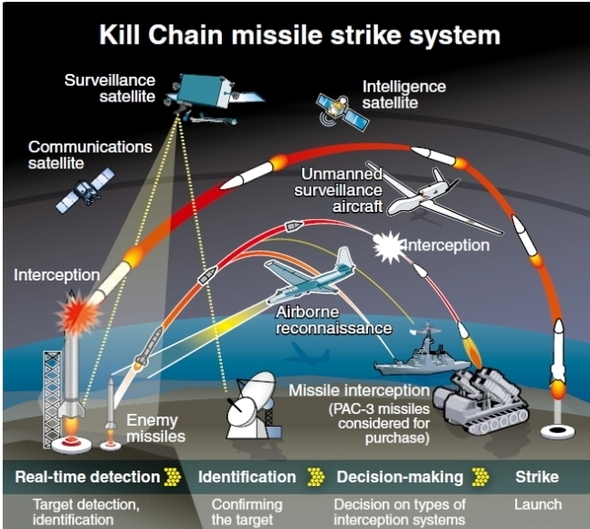
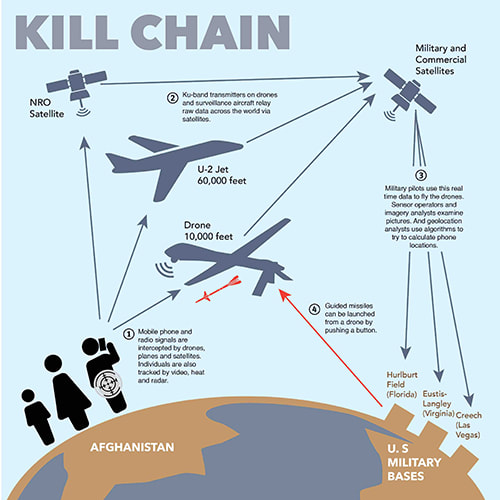
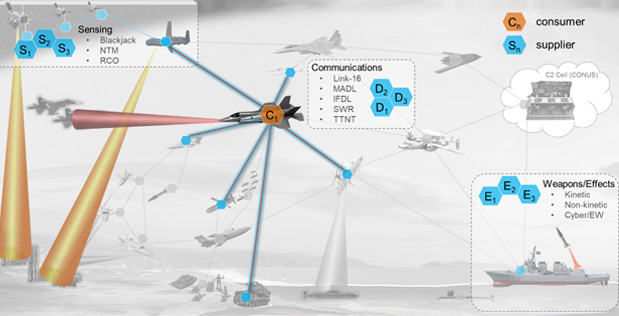
S. Korean military speeds up development of Kill Chain and other response capabilities : North Korea : News : The Hankyoreh

ImpMK on Twitter: "2. The Kill Chain is not for killing North Korean leaders. It is "for striking North Korean nuclear and missile operations systems," including missiles, TELs, the C2 system and
![Lockheed Martin Cyber Kill Chain (CKC) [22] seven steps. The part that... | Download Scientific Diagram Lockheed Martin Cyber Kill Chain (CKC) [22] seven steps. The part that... | Download Scientific Diagram](https://www.researchgate.net/publication/335024682/figure/fig1/AS:789313017098241@1565198296990/Lockheed-Martin-Cyber-Kill-Chain-CKC-22-seven-steps-The-part-that-is-specified-with.png)
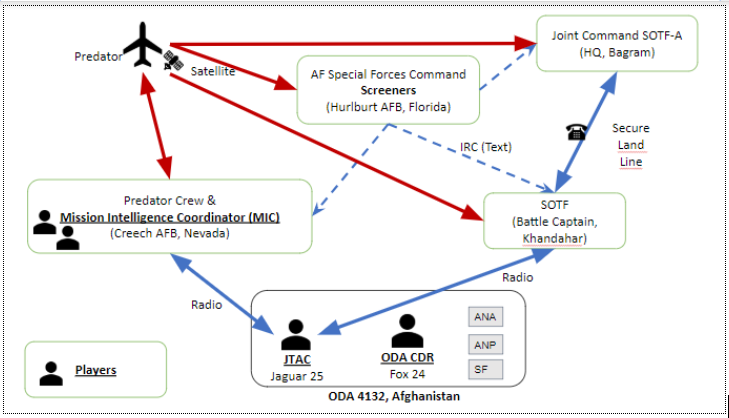



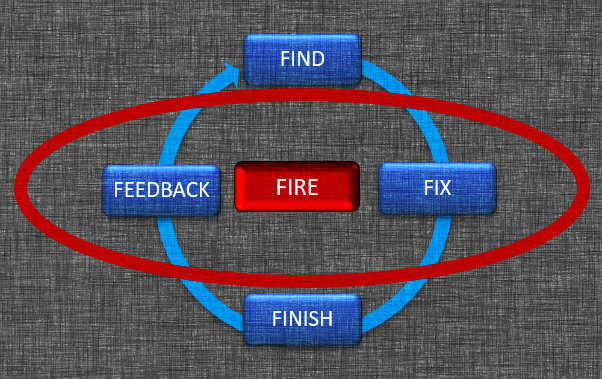
![PDF] Improving the Kill Chain for Prosecution of Time Sensitive Targets | Semantic Scholar PDF] Improving the Kill Chain for Prosecution of Time Sensitive Targets | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e668e73fbc94fb8ebc76ee170dee8a852cb8f60c/3-Figure1-1.png)




![Analysis] The politics of the “kill chain” : International : News : The Hankyoreh Analysis] The politics of the “kill chain” : International : News : The Hankyoreh](https://img.hani.co.kr/imgdb/resize/2013/1023/138241364383_20131023.JPG)