![kassem on Twitter: "Yay, I was awarded a $500 bounty on @Hacker0x01! Bug: Dom based XSS using the swagger ui by [?configUrl=] parameter Tips: ?configUrl=https://t.co/eBpP5NrCqC https://t.co/573zhTCbKG #TogetherWeHitHarder" / Twitter kassem on Twitter: "Yay, I was awarded a $500 bounty on @Hacker0x01! Bug: Dom based XSS using the swagger ui by [?configUrl=] parameter Tips: ?configUrl=https://t.co/eBpP5NrCqC https://t.co/573zhTCbKG #TogetherWeHitHarder" / Twitter](https://pbs.twimg.com/media/FkiHSDCXoA0IzCu?format=jpg&name=large)
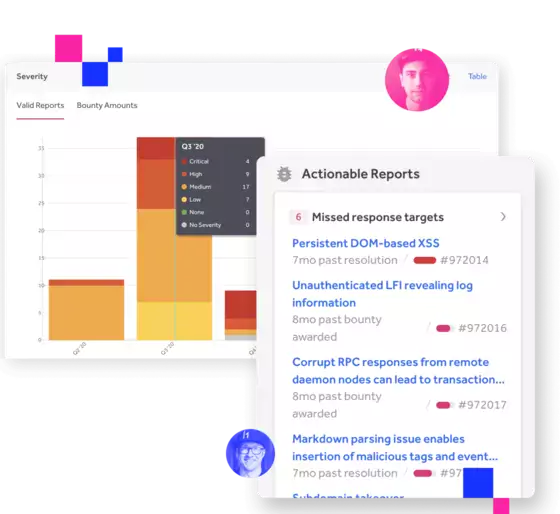
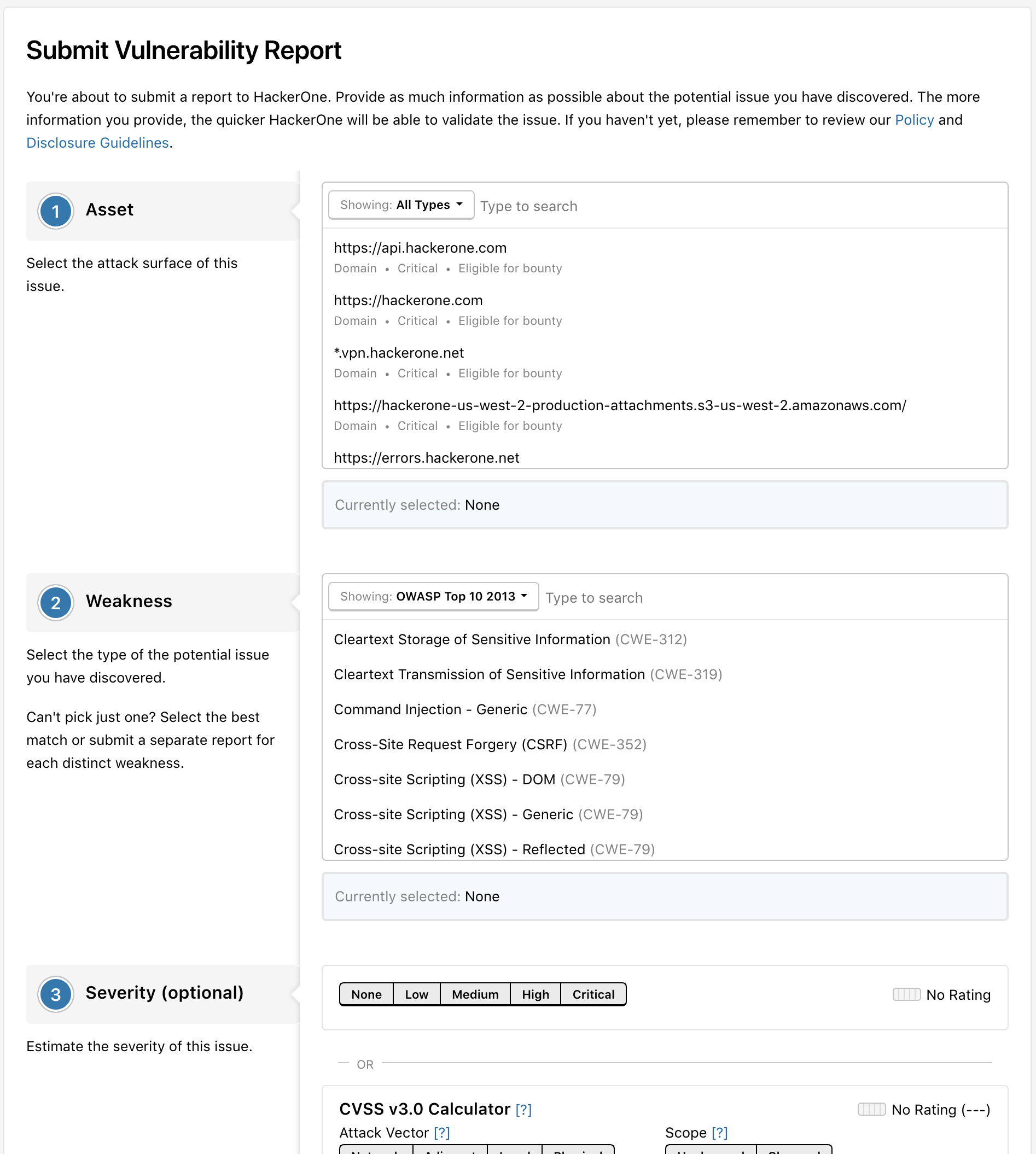
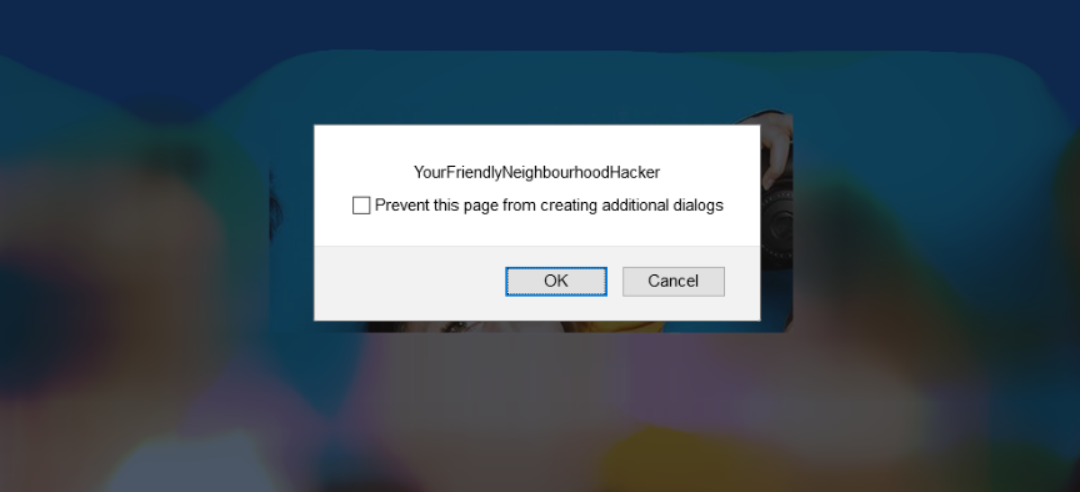
kassem on Twitter: "Yay, I was awarded a $500 bounty on @Hacker0x01! Bug: Dom based XSS using the swagger ui by [?configUrl=] parameter Tips: ?configUrl=https://t.co/eBpP5NrCqC https://t.co/573zhTCbKG #TogetherWeHitHarder" / Twitter
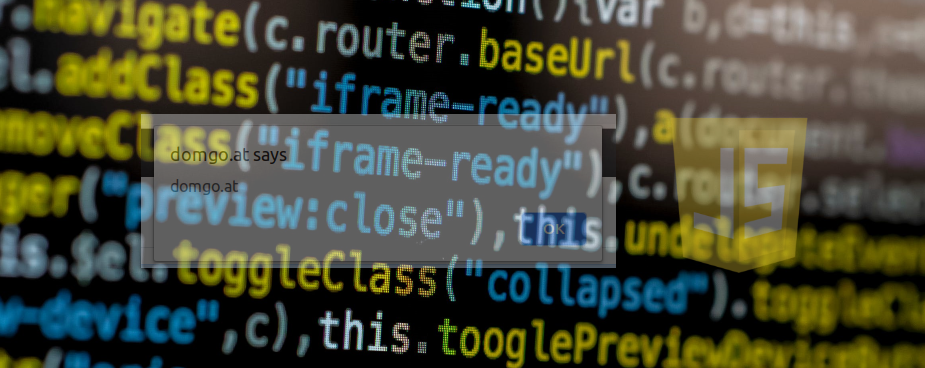
Automating Discovery and Exploiting DOM (Client) XSS Vulnerabilities using Sboxr — Part 2 | by Riyaz Walikar | Appsecco






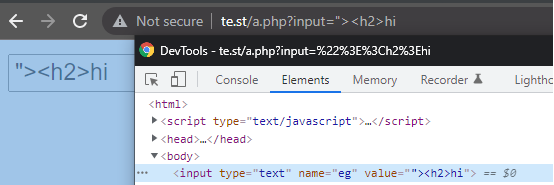

%20attack%20Preview.png)